Domain 7 of CEH: Mobile Platform, IoT, and OT Hacking

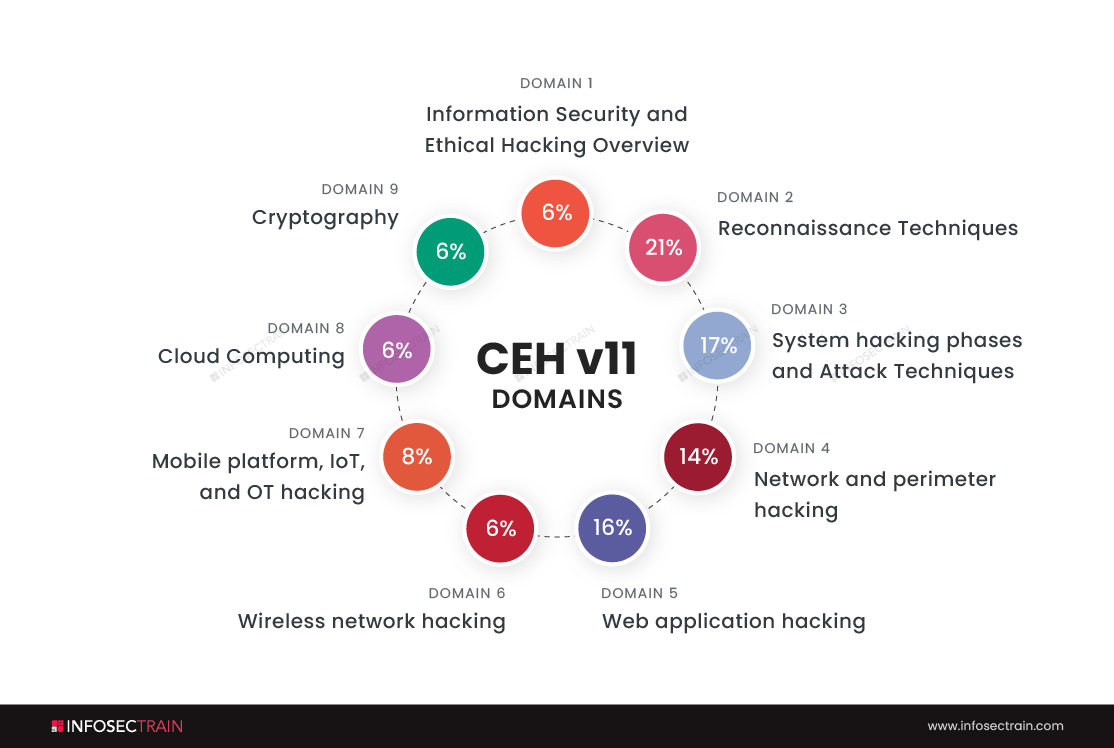
Domains of CEH
- Information Security and Ethical Hacking Overview-6%
- Reconnaissance Techniques-21%
- System hacking phases and Attack Techniques-17%
- Network and perimeter hacking-14%
- Web application hacking-16%
- Wireless network hacking-6%
- Mobile platform, IoT, and OT hacking-8%
- Cloud Computing-6%
- Cryptography-6%
We will discuss the seventh domain of CEH, which is ‘Mobile platform, IoT, and OT hacking.’
Mobile platform hacking
There was an era when people could not come out of their rooms if they were sending some important emails because the computers were not movable. Then came laptops, by which people had the privilege of moving to different locations while working. Yet, it is not so comfortable because laptops can seem like extra baggage while we are traveling. But now, Mobiles have replaced laptops and computers because we can easily send emails, navigate GPS, and browse the Internet with just a 500 grams or less weighing small device. Hence, people are widely using mobiles and storing all their personal and professional information in them.
The latest mobile business innovations have also allowed consumers to carry out transactions such as buying goods and apps over wireless networks, redeeming coupons and tickets, banking, and other services from their mobile phones.
As we are storing a lot of information on our mobile devices, hackers are targeting mobile devices. So organizations are also hiring ethical hackers to make sure there are no vulnerabilities in their products.
The top threats to mobile platforms
Insecure data storage:
- People usually accept all the cookies without checking the cookie policy of that particular website, which may lead to cyber-attacks.
- Being careless while storing data without any security measures can attract hackers and threats.
Errors in cryptography:
- Hacking may happen if there are any errors in cryptographic algorithms.
- If there is poor key management, then there is enormous scope for hacking.
IoT (Internet of Things) hacking
IoT devices are hardware devices in which software, sensors, processing ability, and other technologies are installed. These devices can connect and exchange data over the Internet and any other communication network.
A few examples of IoT devices are:
- Wearable health monitors like smartwatches
- Smart home security systems
- Smart factory equipment
- Biometric scanners
- Autonomous farming equipment
Hacking IoT devices can be remarkably effective because if these devices are hacked, the outcome may cripple our systems, infrastructure, and our lifestyle. Hence, utmost security must be maintained to protect these devices. Organizations are taking a lot of time and effort to test these IoT devices to ensure there are no vulnerabilities.
Ethical hackers are using pretty new tools to hack IoT devices, and the tools are:
Wireshark: Wireshark is an open-source, free packet analyzer that enables you to capture and analyze network traffic in real-time. With the assistance of this tool, we can spy on our targets very easily.
If you and your targets are on the same network, then spying on them is very simple. You just have to open the Wireshark tool and do some configuration settings, and that’s it. You can keep an eye on your target.
Fiddler: Fiddler allows you to step through network traffic between the Internet and test computers to debug web applications. Through the tool, you can examine incoming and outgoing data, so you can monitor and modify requests and responses before the browser receives them.
Nmap: Hackers can use Nmap to gain access to uncontrolled ports on a system. To hack into a targeted system, all a hacker needs to do is run Nmap on it, look for vulnerabilities, and exploit them.
Operational Technology Hacking
Operational Technology (OT) is hardware and software used to detect or alter physical devices, processes, and events through direct monitoring and/or control. In Industrial Control Systems (ICS), OT is widespread, for example, with the SCADA(Supervisory Control and Data Acquisition) system. OT may be used to manage electricity plants or public transit in the field of critical infrastructure. The demand for OT security is growing dramatically as these technologies progress and converge on networked technology.
However, cybercriminals have typically been interested in stealing data, but they have recently begun focusing more on OT networks, realizing the potential for disruption due to inadequate OT security. This has led to the emergence of sophisticated and destructive attacks specific to the operational technology sector.
OT organizations are aware of this danger. Recently, the SANS Institute surveyed OT security professionals who said the risk is at critical levels. According to the 2016 State of Operational Technology Report, nearly 74% of OT organizations experienced malware intrusions in the past 12 months, resulting in damaged productivity, revenue, brand trust, intellectual property, and physical security.
Want to know more about mobile platforms, IoT, and OT hacking? Join InfosecTrain
CEH with InfosecTrain
InfosecTrain is one of the leading training providers with a pocket-friendly budget. We invite you to join us for an unforgettable journey with industry experts to gain a better understanding of the Certified Ethical Hacker course can be taken as live instructor-led sessions or as self-paced courses, allowing you to complete your training journey at your convenience.





 1800-843-7890 (India)
1800-843-7890 (India) 
