Domain 9 of CEH: Cryptography
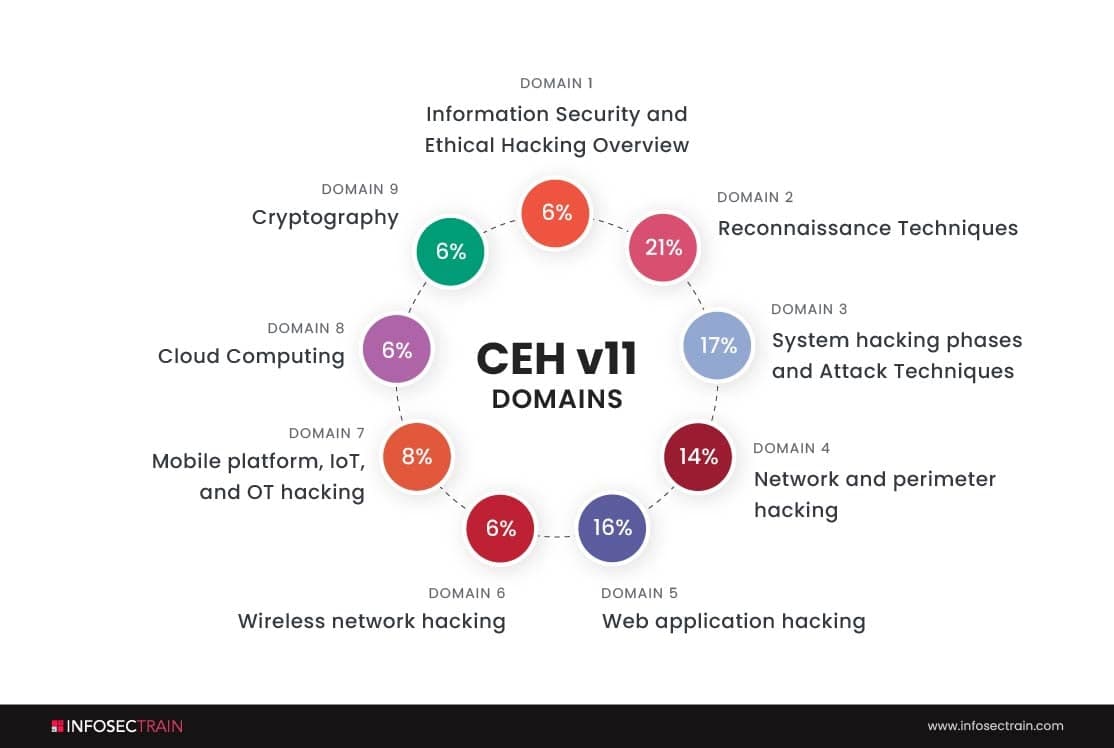
Domains of CEH
- Information Security and Ethical Hacking Overview-6%
- Reconnaissance Techniques-21%
- System hacking phases and Attack Techniques-17%
- Network and perimeter hacking-14%
- Web application hacking-16%
- Wireless network hacking-6%
- Mobile platform, IoT, and OT hacking-8%
- Cloud Computing-6%
- Cryptography-6%
We will discuss the ninth domain of CEH, which is ‘Cryptography.’
What is cryptography?
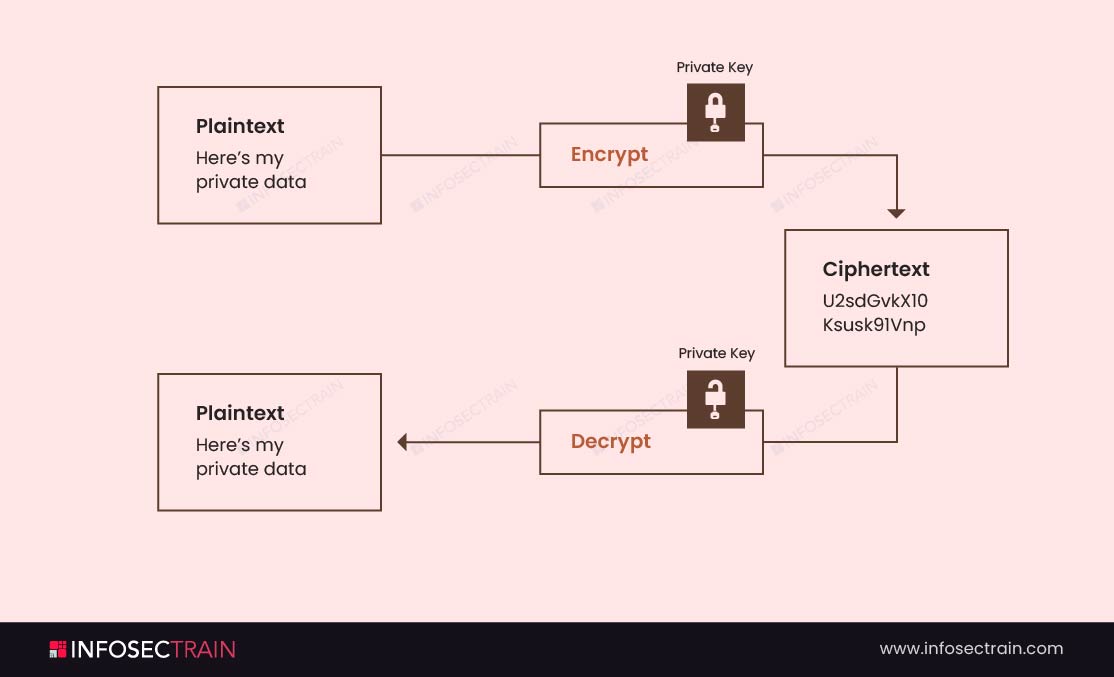
Cryptography is a technique through which we can convert plain text into ciphertext and can convert the ciphertext into plain text. Didn’t get my point? No worries! Let me give you a simple example.
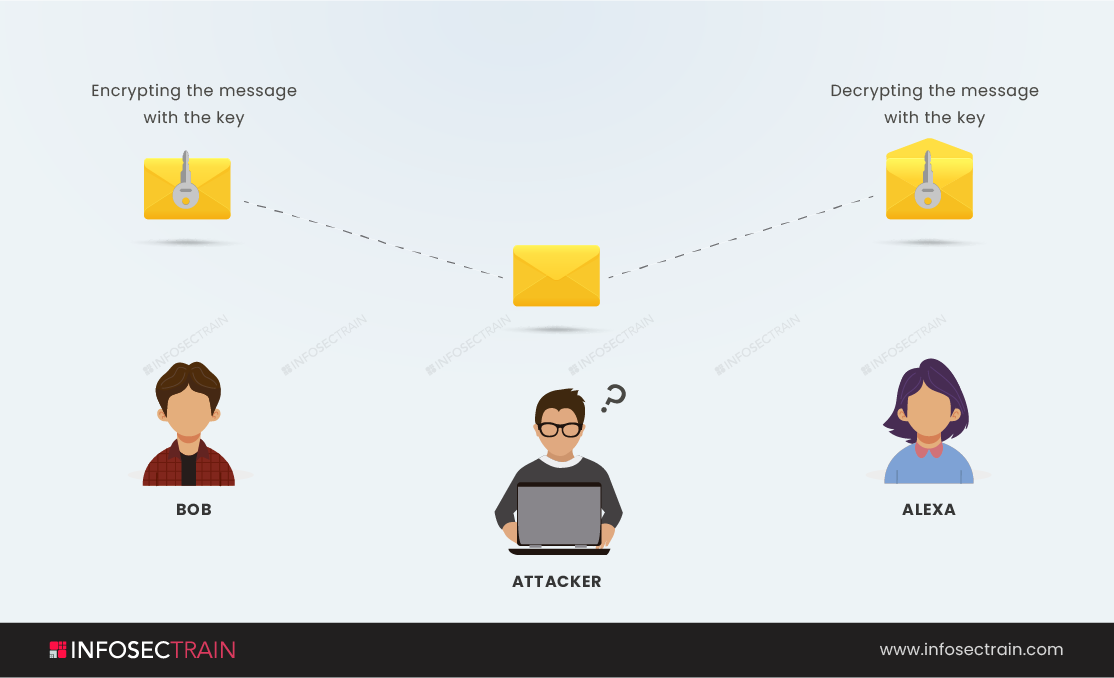
Assume there are two friends staying in different corners of the world. And, one of them (let’s say Bob) is sending a piece of confidential information to another (let’s say, Alexa). Now, in between, some attackers may access this information to avoid this by Using a key, Bob may convert the plain text (original message) into ciphertext (a combination of random numbers and alphabets). Now, even if the attacker finds the message, he will not understand it. And finally, after receiving the message, Alexa can use the key to convert the ciphertext into plaintext. This entire process of converting the texts to maintain their secrecy is called cryptography.
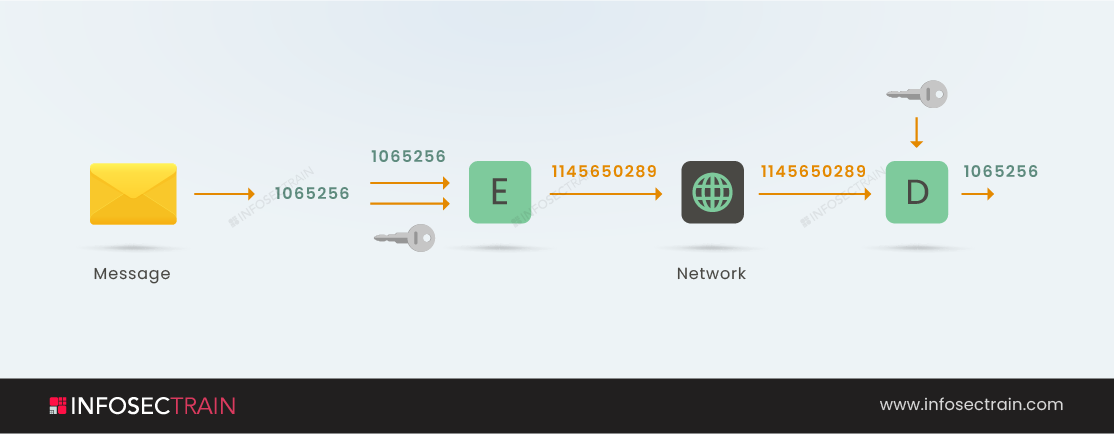
As shown in the figure, the original message is 1065256; this message is applied to an encryption key. This key is used in the encryption algorithm by which the message is converted in a ciphertext (unreadable format), This ciphertext will be sent across the network to the other end of the world. The other person for whom the message is sent will use a decryption key and ciphertext as a parameter of the decryption algorithm and get the original message (1065256).
Keys? What keys? Is this your question? Then go further.
Keys
In cryptography, keys are strings of characters (combinations of letters, numbers, and symbols) used in an encryption algorithm for altering data so that it appears random. Just like physical keys, these keys also lock (encrypt) the data, and only someone with the correct key can unlock (decrypt) the data.
Objectives of cryptography
Cryptography concentrates on four different objectives.
- Non-repudiation: This term refers to a message that can never be retracted by the sender or taken back.
- Confidentiality: Private communications are protected by confidentiality, ensuring the intended recipient can only read the message after it has been decrypted.
- Authenticity: Authenticity helps ensure that both senders and recipients can verify each other’s identities and that the intended recipients have received the message.
- Integrity: Integrity is the ability to ensure that the information in a message cannot be modified while it is being stored or transported.
Types of Cryptography
Symmetric key cryptography: Symmetric key cryptography or symmetric encryption is an algorithm for cryptography that utilizes the same cryptographic key for both the plaintext’s encryption plus the ciphertext’s decryption. The keys may be related, or there may be a slight variation between the two keys.
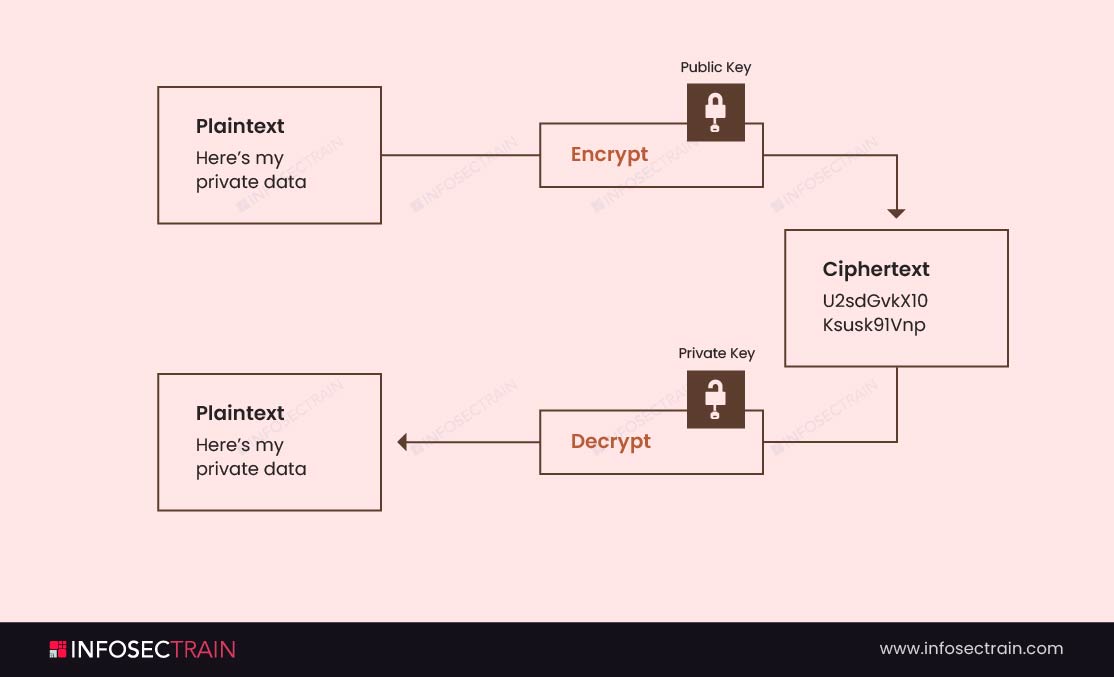
Asymmetric key cryptography: Asymmetric cryptography, also called public-key cryptography, is a process that encrypts and decrypts a message with two related keys, one public and one private, to prevent unauthorized access or use of confidential information.
The importance of cryptography
- Privacy: Whether we are talking about the digital or physical worlds, privacy is all we care about. I’m not sure about the physical world, but cryptography can give us privacy in the digital universe. By encrypting our data, we ensure that only legitimate users can view it, and hackers, cybercriminals, internet providers, and even government agencies cannot access our data.
- Authentication: In cryptography, we scramble our original data using a random passcode, called an encryption key, in order to protect it. Using this key eliminates the possibility that others will access your data. Sometimes hackers pretend to be authorized users in order to gain access. So, making the encryption key authenticated will protect your data.
CEH with InfosecTrain
InfosecTrain is one of the leading training providers with a pocket-friendly budget. We invite you to join us for an unforgettable journey with industry experts to gain a better understanding of the Certified Ethical Hacker course. Courses can be taken as live instructor-led sessions or as self-paced courses, allowing you to complete your training journey at your own convenience.





 1800-843-7890 (India)
1800-843-7890 (India)