CompTIA Security+ Training in Kenya
 Read Reviews
Read Reviews
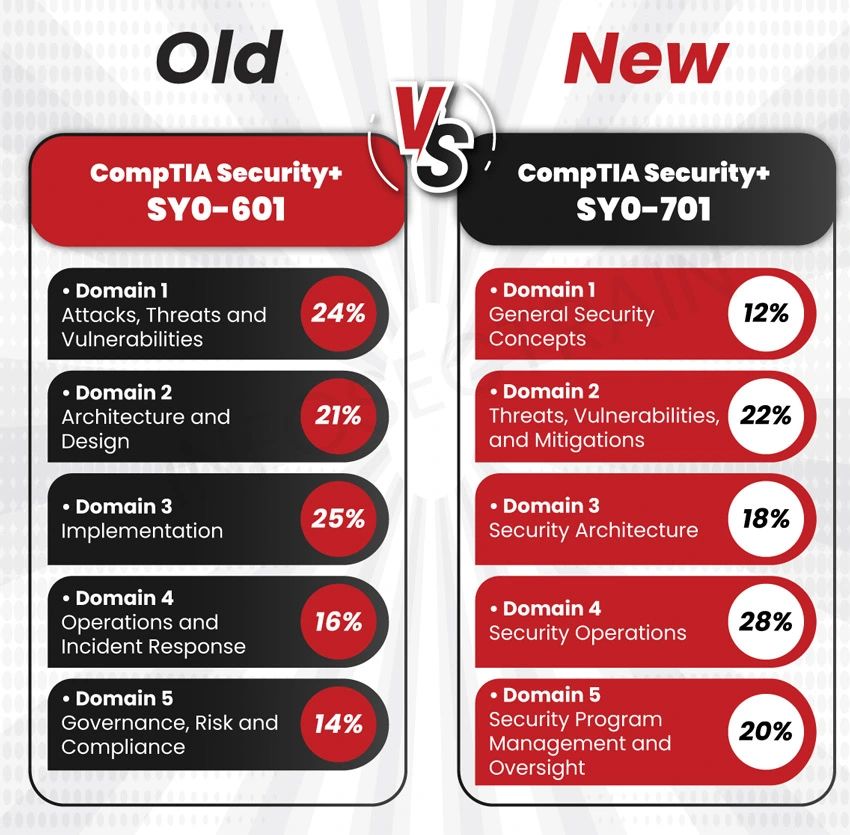
In the ever-evolving cybersecurity landscape, the latest version of the CompTIA Security+ (SY0-701) training course in Kenya from InfosecTrain is your gateway to mastering the core skills necessary to secure data and information systems in the digital age. With a focus on the latest threats, automation, zero trust principles, IoT security, risk management, and more, this course equips participants to pass the Security+ SY0-701 exam in Kenya on their first attempt.



 5th Sep: Weekend
5th Sep: Weekend 




 I want to express my deepest gratitude to Trainer, who helped me to pass my exam. The Trainer went the extra mile to assist me, and I have gained a significant benefit because of his knowledge and skills in Information Security. Infosec Train, you are a pioneer in the community and
I want to express my deepest gratitude to Trainer, who helped me to pass my exam. The Trainer went the extra mile to assist me, and I have gained a significant benefit because of his knowledge and skills in Information Security. Infosec Train, you are a pioneer in the community and







 1800-843-7890 (India)
1800-843-7890 (India)